| This is a Publication |
 |
 |
INFOGRAPHIC
When you work in the cloud, your organization needs real-time threat�prevention technologies and services across your applications. The more
digitally connected you are, the greater your risk of cyberattacks
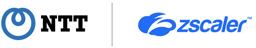
In the past, users or devices inherited trust and access to certain resources when they connected to an
on-campus network by plugging in a network cable or connecting via a virtual private network.
Now, we verify upon each connection that there really is a valid and authorized user behind that request.
|
| What is zero trust security? |
 |
To achieve your business goals, you need an agile and
predictive security ecosystem across your users, devices,
applications and infrastructure.
We manage your risks and minimize your downtime with
our integrated cybersecurity services. Supported by Palo
Alto Networks, we protect your network, endpoints, and
cloud and mobile applications, and help you to prevent,
predict, detect and respond to cyberthreats. |
| |
|
|
|